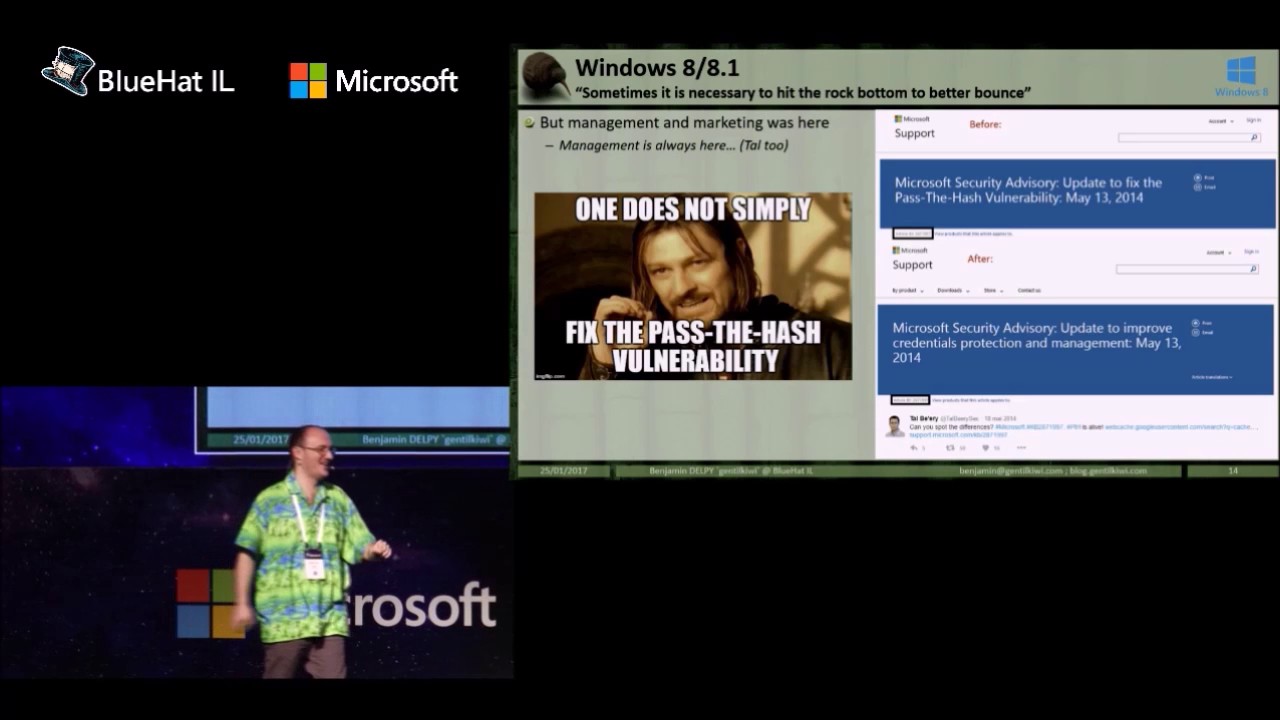
BlueHat IL 2019 - Benjamin Delpy (@gentilkiwi) - You (dis)liked mimikatz? Wait for kekeo
Автор: Microsoft Israel R&D Center
Загружено: 2019-02-18
Просмотров: 8246
Описание:
For years, you’ve tried to fight mimikatz, first to understand it, and maybe fight it again.
This little kiwi fruit shaped program has given you a hard time, extracted your password, stolen your credentials, played with your nerves and certificates ...
But our friends in New Zealand know it best: there are many different kiwis... and perhaps the fruit is the most lucrative, but it's not the most sadistic.
The kiwi animal may not fly, and it remains complex to build it from source, its effects are not less devastating...I will introduce "kekeo", the little animal brother of mimikatz.
If you enjoyed playing with Kerberos, ASN1, security providers..., then you'll love adopting this furry, sweet animal. From its birth with MS14-068 to cleartext passwords without local administrator rights, you'll know everything about this animal.
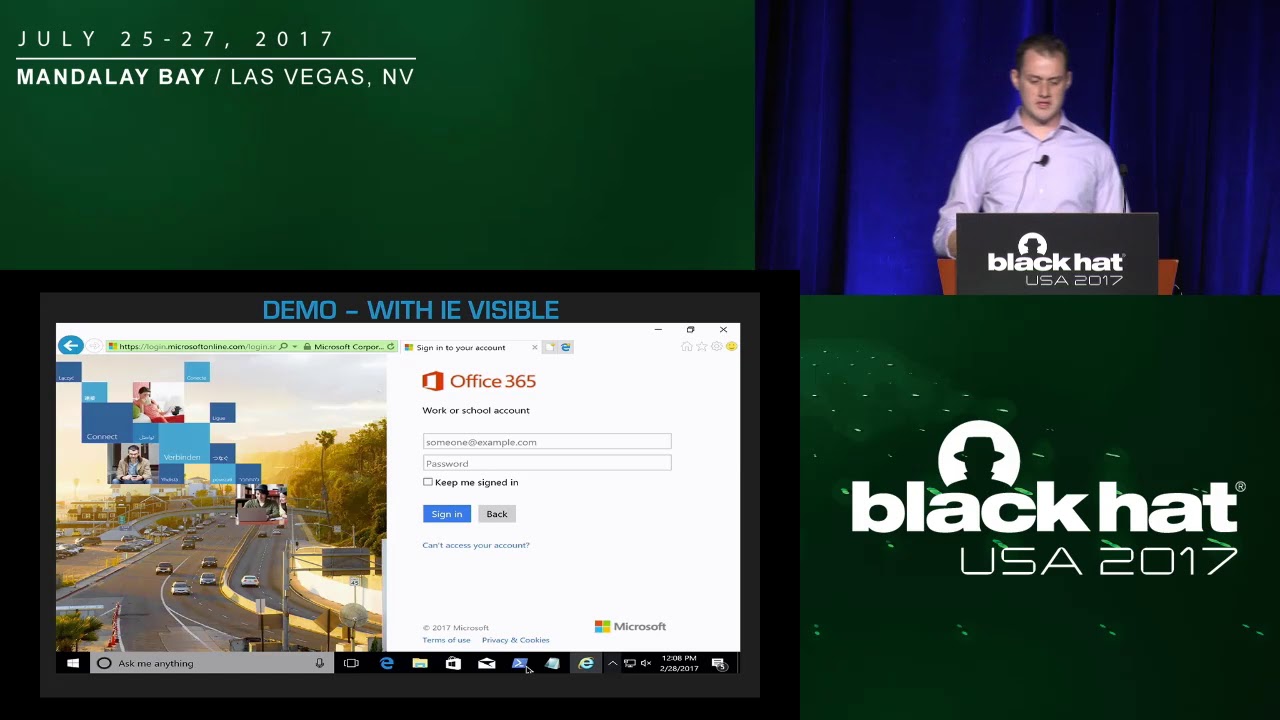
This talk will embed CredSSP and TSSP with cleartext credential, explore a little bit about PKINITMustiness and the RSA-on-the-fly for Kerberos with PKI!
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: