Black Hat USA 2025 | Digital Dominoes: Scanning the Internet to Expose Systemic Cyber Risk
Автор: Black Hat
Загружено: 2026-03-08
Просмотров: 810
Описание:
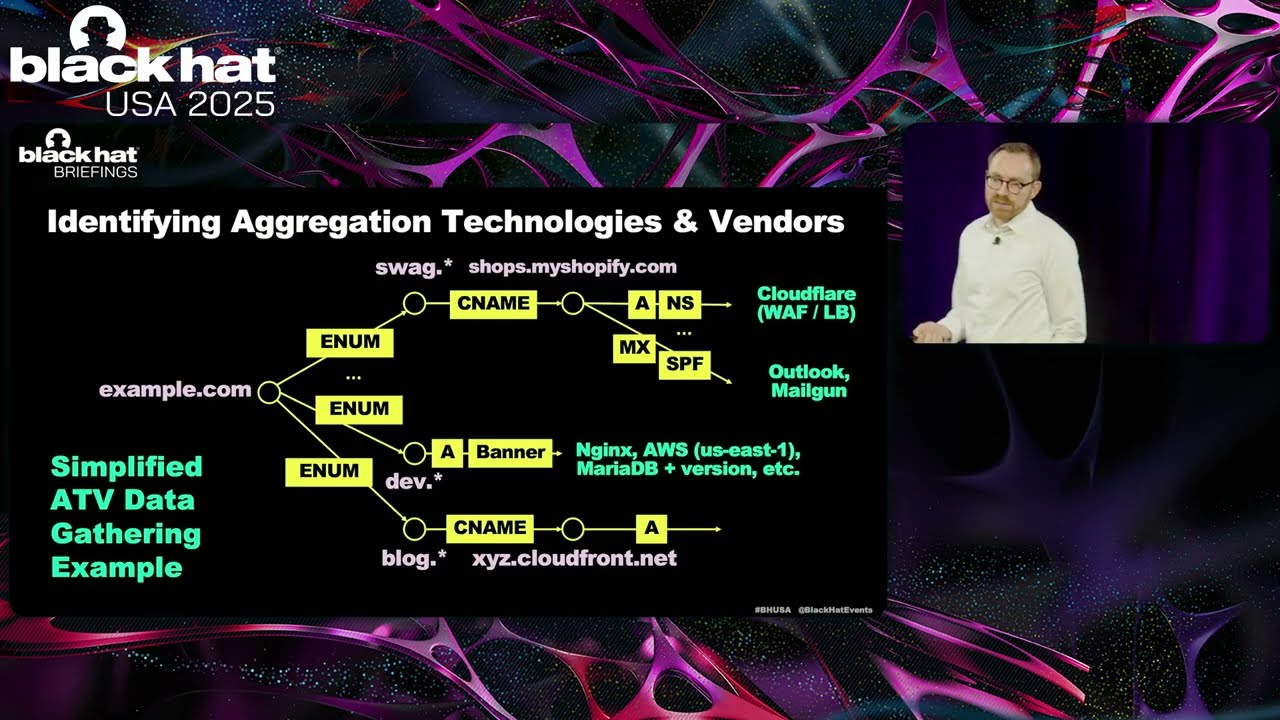
Policymakers and risk owners face significant challenges in managing systemic cyber risk, largely because few tools use empirical data to accurately identify and quantify it. But that data is essential to (1) identify vendors and technologies that require targeted measures, (2) track how systemic cyber threats evolve compared to non-cyber risk, and (3) assess the effectiveness of targeted interventions. Traditional approaches rely on backward-looking models or hypothetical scenarios—methods that can't keep pace with today's fast-moving, complex digital infrastructure. What's needed are real-time, data-driven insights that empower decision-makers to take meaningful action.
We address this gap by leveraging internet-scale scanning to build a dynamic, empirical map of concentration risk—showing how systemic vulnerabilities spread across networks, technologies, and vendors. In a first-of-its-kind live demonstration, we will unveil a new risk visualization platform that highlights how risk concentrates within and across sectors, including those supporting critical national functions.
Our findings challenge conventional wisdom. Many assumed sources of systemic risk have limited real-world impact, while some overlooked technologies (e.g., large industry-specific white label SaaS vendors) carry significant potential for cascading failures across society. Drawing from real-world examples in sectors such as financial services and manufacturing, we demonstrate how this platform—and the dynamic models behind it—can support more informed, data-driven policy interventions. Participants will leave with a clearer understanding of the systemic risk landscape, as well as actionable insights for developing smarter, more resilient national cyber strategies.
Participants will be able to:
Define the Unseen: Understand systemic cyber risk in the real world—down to specific technologies, vendors, and interdependencies in the digital supply chain.
Track, Quantify, Predict: Monitor how cyber threats evolve, compare risk levels across sectors, and assess impact alongside traditional risk categories.
Test What Works: Evaluate potential policy interventions using dynamic, empirical models grounded in real infrastructure data—not theoretical scenarios.
By:
Morgan Hervé-Mignucci | Head of ERM Analytics, Coalition, Inc.
Presentation Materials Available at:
https://blackhat.com/us-25/briefings/...
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: