Black Hat USA 2025 | Detecting Taint-Style Vulnerabilities in Microservice-Structured Web Apps
Автор: Black Hat
Загружено: 2026-03-08
Просмотров: 903
Описание:
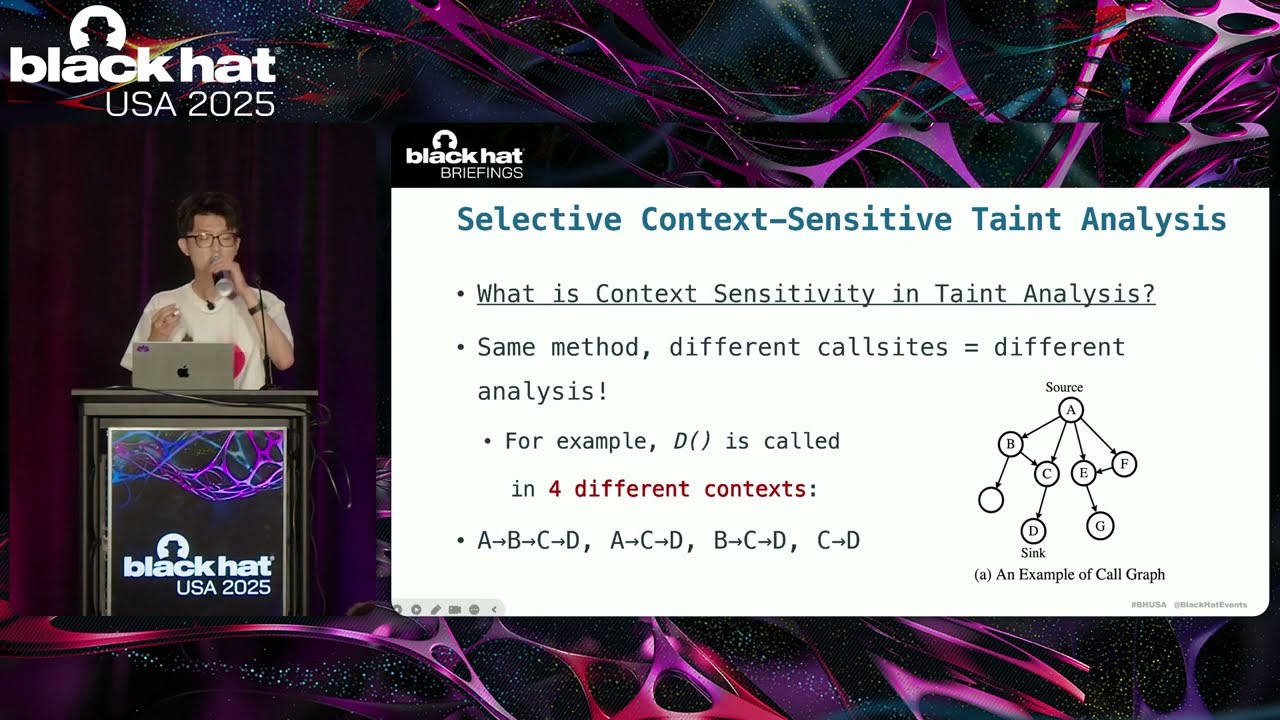
Microservice architecture has become increasingly popular for building scalable and maintainable applications. A microservice-structured web application (shortened to microservice application) enhances security by providing a loose-coupling design and enforcing the security isolation between different microservices. However, in this paper, our study shows microservice applications still suffer from taint-style vulnerability, one of the most serious vulnerabilities (e.g., code injection and arbitrary file write). We propose a novel security analysis approach, named MTD, that can effectively detect taint-style vulnerabilities in real-world, evolving-fast microservice applications. Our approach mainly consists of three phases. First, MTD identifies the entry points accessible to external malicious users by applying a gateway-centric analysis. Second, MTD utilizes a new data structure, i.e., service dependence graph, to bridge inter-service communication. Finally, MTD employs a distance-guided strategy for selective context-sensitive taint analysis to detect vulnerabilities.
To validate the effectiveness of MTD, we applied it to 25 open-source microservice applications (each with over 1,000 stars on GitHub) and 5 industrial microservice applications from a world-leading fintech company, i.e., Alibaba Group. We found that MTD effectively vetted these applications, discovering 59 high-risk zero-day vulnerabilities. Among these, vulnerabilities in open-source applications resulted in the allocation of 31 CVE identifiers, including CVE-2024-22263 in the Spring Projects, which has a CVSS score of 9.8. In the industrial microservice applications, we discovered 20 vulnerabilities, including groovy code injection and arbitrary command execution. These vulnerabilities could compromise the entire web server, severely affecting the integrity of millions of users' private data and the security of company systems. MTD effectively detected these high-value vulnerabilities (worth $50,000 in bounties) and successfully safeguarded enterprise security.
By:
Fengyu Liu | Ph.D Student, Fudan University
YouKun Shi | Postdoctoral Researcher, Hong Kong Polytechnic University
Tian Chen | Master's Student, Fudan University
Bocheng Xiang | Fudan University
Junyao He | Senior Security Engineer, Alibaba Group
Qi Li | Senior Security Engineer, Alibaba Group
Guangliang Yang | Assistant Professor, Fudan University
Yuan Zhang | Professor, Fudan University
Min Yang | Professor, Fudan University
Presentation Materials Available at:
https://blackhat.com/us-25/briefings/...
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке:



















