Видео с ютуба Heapbleed

Patroklos Argyroudis Project Heapbleed

Black Hat USA 2010: Understanding Fragmentation Heap: From Allocation to Exploitation 1/4

DEF CON 26 - Sanat Sharma - House of Roman a Leakless Heap Fengshui to Achieve RCE on PIE Binaries

Dedup Est Machina: Memory Deduplication as an Advanced Exploitation Vector

#HITB2012AMS D2T2 - Steven Seeley - Ghost in the Windows 7 Allocator
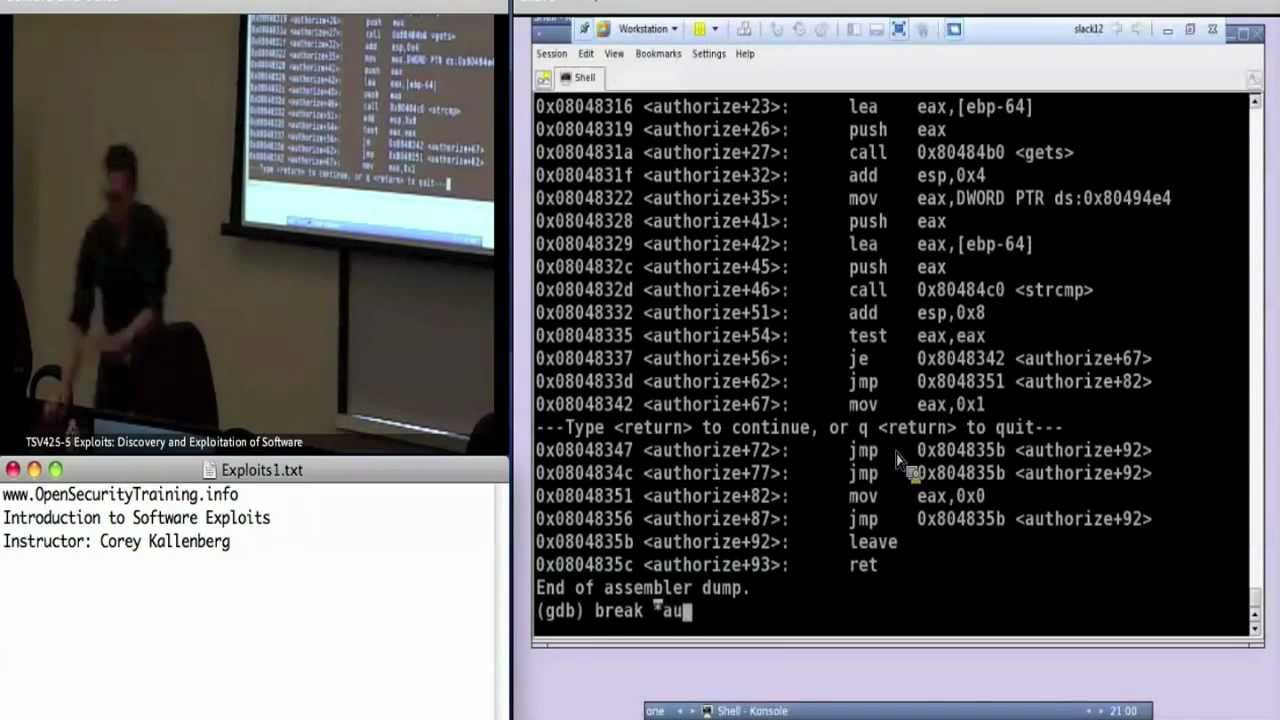
Day 1 Part 4: Exploits1: Introduction to Software Exploits

ZeroNights 2014 Patroklos Argyroudis Project Heapbleed

Black Hat USA 2012 - Exploiting The Jemalloc Memory Allocator: Owning Firefox's Heap

DEFCON 15: Remedial Heap Overflows: dlmalloc style

#HITBGSEC 2018 D1: Turning Memory Errors Into Code Execution With Client-Side Compilers - R. Gawlik

RuhrSec 2019: "Greybox Automatic Exploit Generation for Heap Overflows", Sean Heelan

REcon 2014 25 - Exploit tips and techniques (William Peteroy)

Thirty Seven Colossal SCTP Facts Every Executive Must Know

GOFA

BalCCon2k14 - Aleksandar Pejic & Andrija Prcic - Embedded Linux device drivers
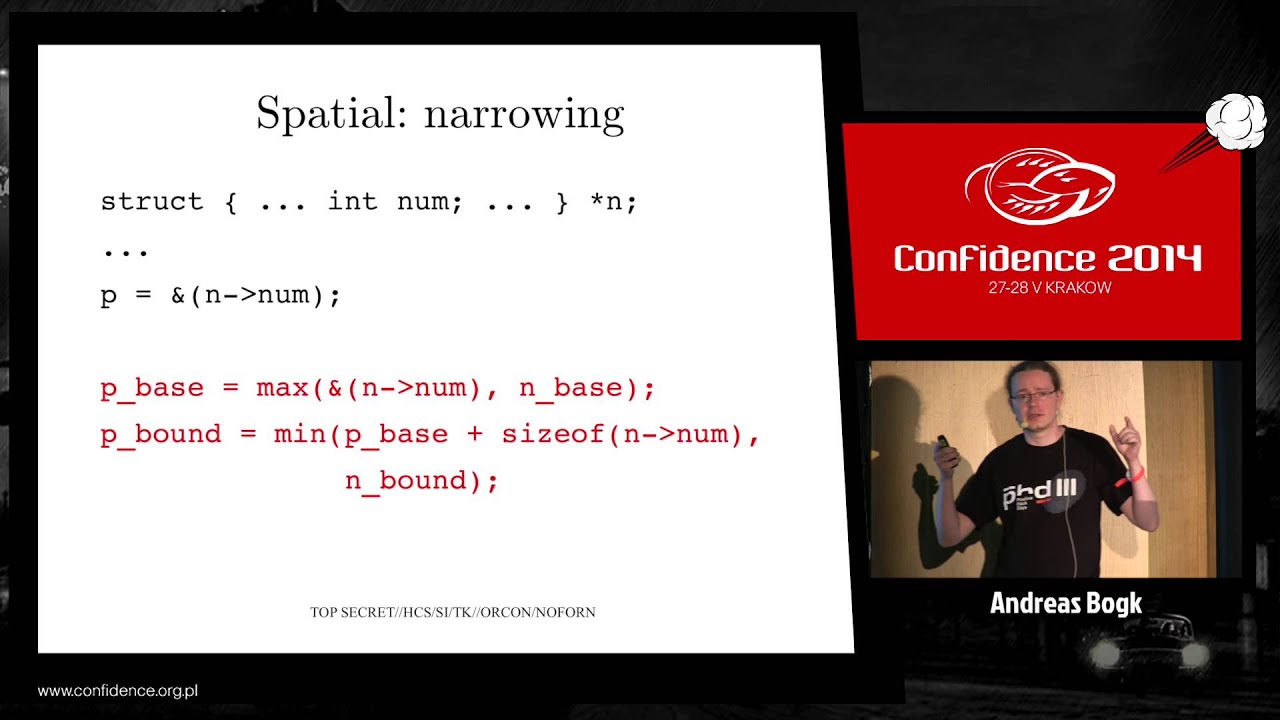
CONFidence 2014: Preventing violation of memory safety in C/C++ software - Andreas Bogk

Understanding & Breaking The Heap
![[AthCon 2011] Introducing The Parasite](https://imager.clipsaver.ru/yTkIsdFFHR0/max.jpg)
[AthCon 2011] Introducing The Parasite

BalCCon2k14 - Mitch Altman - OpenSource Hardware

Guida veloce al... ehm, alt.rock/post-grunge.