Mastering Microsoft Defender: Endpoint + Cloud Apps Integration Explained PART-1
Автор: rijoskill
Загружено: 2025-08-04
Просмотров: 591
Описание:
Mastering Microsoft Defender: Endpoint + Cloud Apps Integration Explained | PART-1
Welcome to *Part 1* of our comprehensive series on *Mastering Microsoft Defender**, where we take a deep dive into the integration of **Microsoft Defender for Endpoint* with **Microsoft Defender for Cloud Apps**. This video is designed to help IT professionals, security analysts, and cloud architects understand how to leverage Microsoft’s powerful security tools to build a robust, unified threat protection strategy across endpoints and cloud environments.
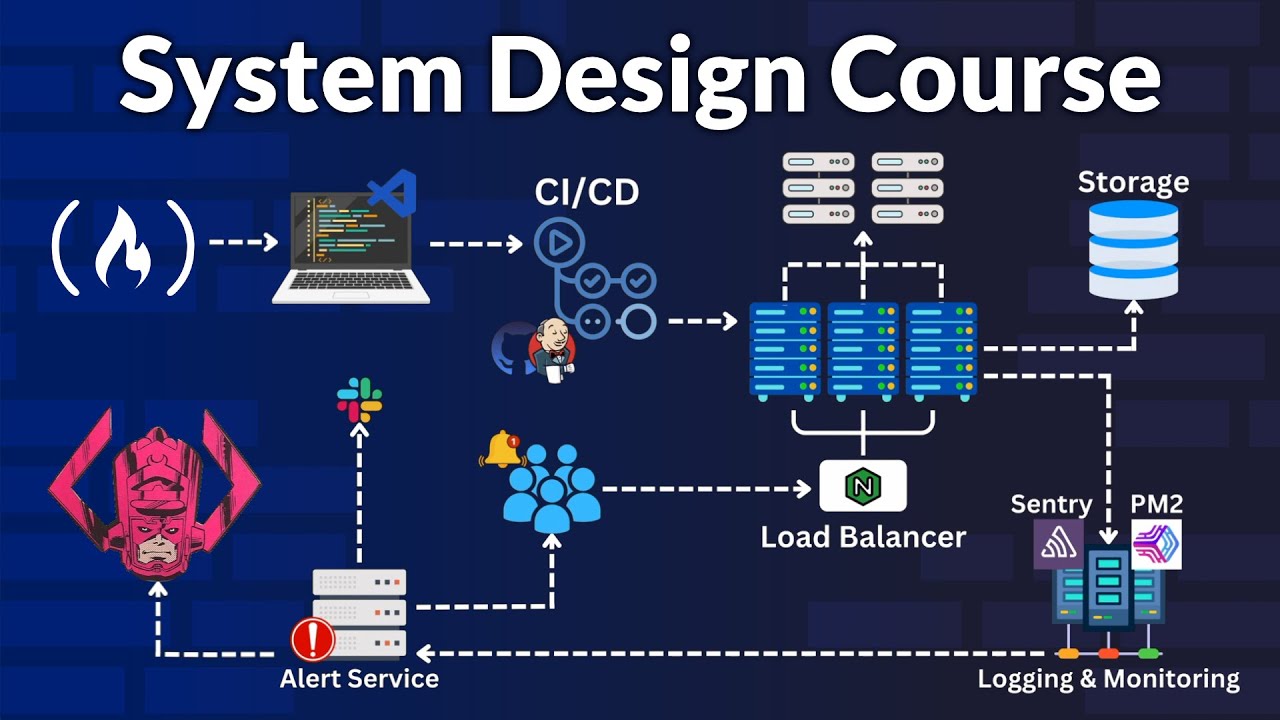
In today’s digital landscape, organizations face increasingly sophisticated cyber threats that target both on-premises devices and cloud-based applications. Microsoft Defender offers a suite of tools that, when properly integrated, can provide end-to-end visibility, automated threat detection, and coordinated response capabilities. This video focuses on the *foundational integration* between Defender for Endpoint and Defender for Cloud Apps—two critical components of Microsoft’s extended detection and response (XDR) ecosystem.
What This Video Covers
In this first installment, we walk through the *core concepts, setup process, and strategic value* of integrating these two Defender solutions. Here's a breakdown of what you'll learn:
Introduction to Microsoft Defender Ecosystem
Overview of Microsoft’s XDR strategy
Key components: Defender for Endpoint, Defender for Cloud Apps, -- Defender for Identity, and Defender for Office 365
Why integration matters: unified threat intelligence, streamlined workflows, and reduced response time
Microsoft Defender for Endpoint
What it is: an enterprise-grade endpoint detection and response (EDR) solution
Capabilities: real-time threat detection, behavioral analysis, vulnerability management, and automated remediation
Supported platforms: Windows, macOS, Linux, Android, and iOS
Microsoft Defender for Cloud Apps
What it is: a cloud access security broker (CASB) that provides visibility and control over cloud applications
Capabilities: app discovery, data protection, threat detection, and compliance monitoring
Integration with Microsoft 365, Azure, AWS, Google Workspace, and more
Why Integration Is Crucial
Integrating Defender for Endpoint with Defender for Cloud Apps creates a synergistic security model** that enhances visibility and control across your entire digital estate. Here’s why this integration is a game-changer:
Unified Threat Detection Endpoint signals can trigger cloud app investigations, and vice versa.
-Contextual Insights Correlate device risk levels with cloud app usage to identify suspicious behavior.
-Automated ResponseUse Conditional Access policies to block risky users or devices from accessing sensitive cloud resources.
Improved ComplianceMonitor and enforce data governance policies across endpoints and cloud apps.
Step-by-Step Integration Guide
In this video, we walk through the *configuration process* to connect Defender for Endpoint with Defender for Cloud Apps:
1. Prerequisites
Microsoft 365 E5 or equivalent licensing
Defender for Endpoint and Defender for Cloud Apps enabled
Admin access to Microsoft 365 Security Center and Microsoft Defender portal
2. Enable Device Discovery in Defender for Cloud Apps
Navigate to the Cloud Apps portal
Enable integration with Defender for Endpoint
Configure discovery settings to collect endpoint telemetry
3. Configure Endpoint Settings
Ensure Defender for Endpoint is actively monitoring devices
Enable cloud app discovery in the Endpoint portal
Validate that endpoint signals are flowing into Cloud Apps
4. Verify Integration
Check the Cloud Discovery dashboard
Review discovered apps and user activity
Monitor alerts triggered by endpoint-cloud correlation
Real-World Use Cases
We also explore practical scenarios where this integration delivers measurable security benefits:
#MicrosoftDefender, #DefenderForEndpoint, #DefenderForCloudApps, #Microsoft365Security, #CyberSecurity, #EndpointSecurity, #CloudSecurity, #XDR, #CASB, #ThreatDetection, #SecurityIntegration, #MicrosoftTutorial, #ShadowIT, #ConditionalAccess, #CloudDiscovery
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке:










![Hackers Love Your Default Defender Setup [Fix: Copy These Settings]](https://imager.clipsaver.ru/R8btJ_SjwVk/max.jpg)