$50,000 0-day RCE on Apple bug bounty program
Автор: Bug Bounty Reports Explained
Загружено: 2021-06-14
Просмотров: 18778
Описание:
Sign up for Intigriti: https://go.intigriti.com/bbre
📧 Subscribe to BBRE Premium: https://bbre.dev/premium
✉️ Sign up for the mailing list: https://bbre.dev/nl
📣 Follow me on Twitter: https://bbre.dev/tw
🖥 Get $100 in credits for Digital Ocean 🖥
https://m.do.co/c/cc700f81d215
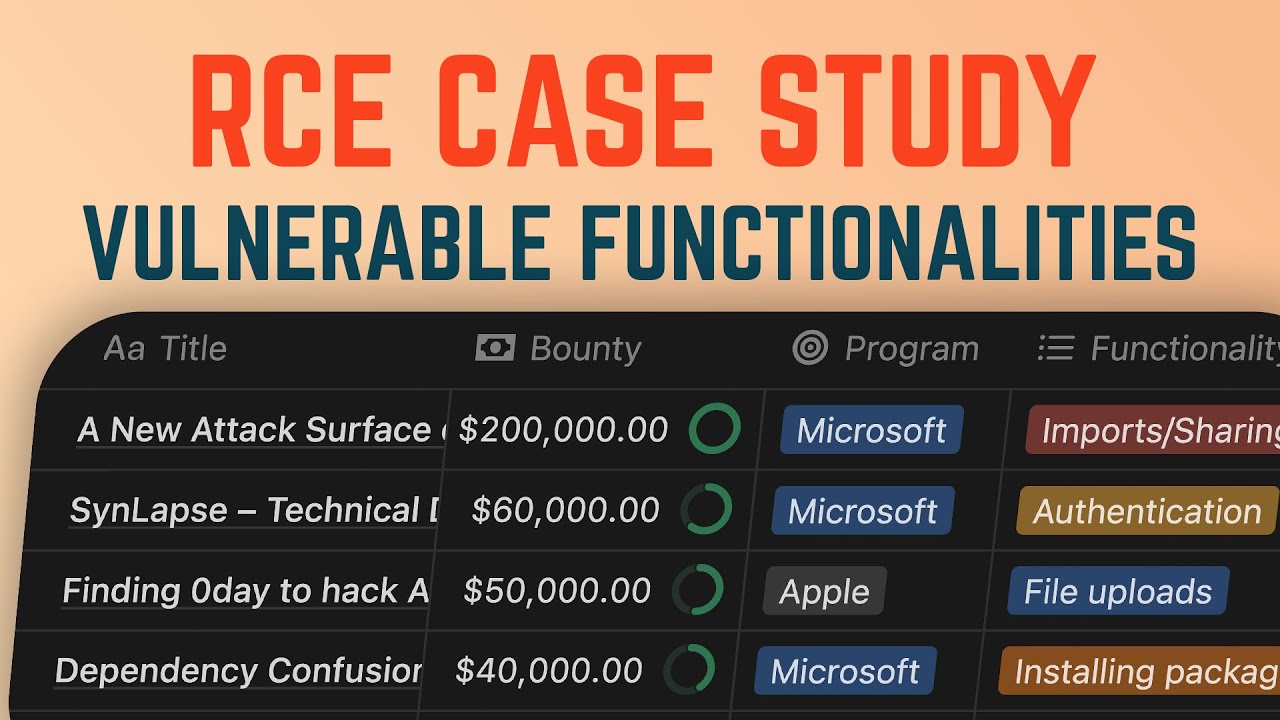
This video is an explanation of a bug bounty report by Harsh Jaiswal and Rahul Maini that resulted in an RCE (Remote Code Execution) on Apple bug bounty program. The vulnerability was a 0-day in Lucee server. It was later assigned the CVE-2021-21307.
✎Sign up for Pentesterlab from my referral✎
https://pentesterlab.com/referral/Vtc...
Report:
https://github.com/httpvoid/writeups/...
Reporter's twitter:
/ rootxharsh
/ iamnoooob
Follow me on twitter:
/ gregxsunday
Commit with the fix:
https://github.com/lucee/Lucee/commit...
Timestamps:
00:00 Intro
00:21 Intigriti - the sponsor of this video
00:59 Lucee server
02:41 The "easy" RCE
04:30 Bypassing Apple WAF
06:18 The exploit step-by-step
08:40 The reward and the fix
#RCE #CVE-2021-21307
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: