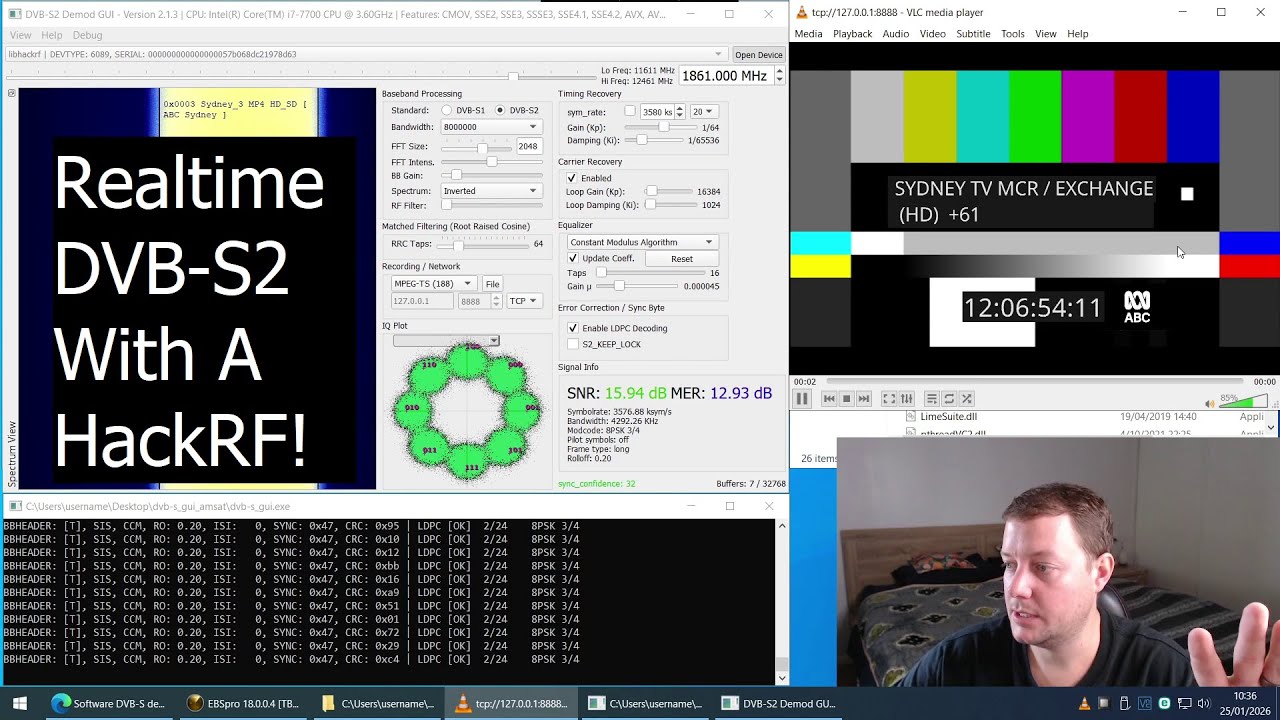
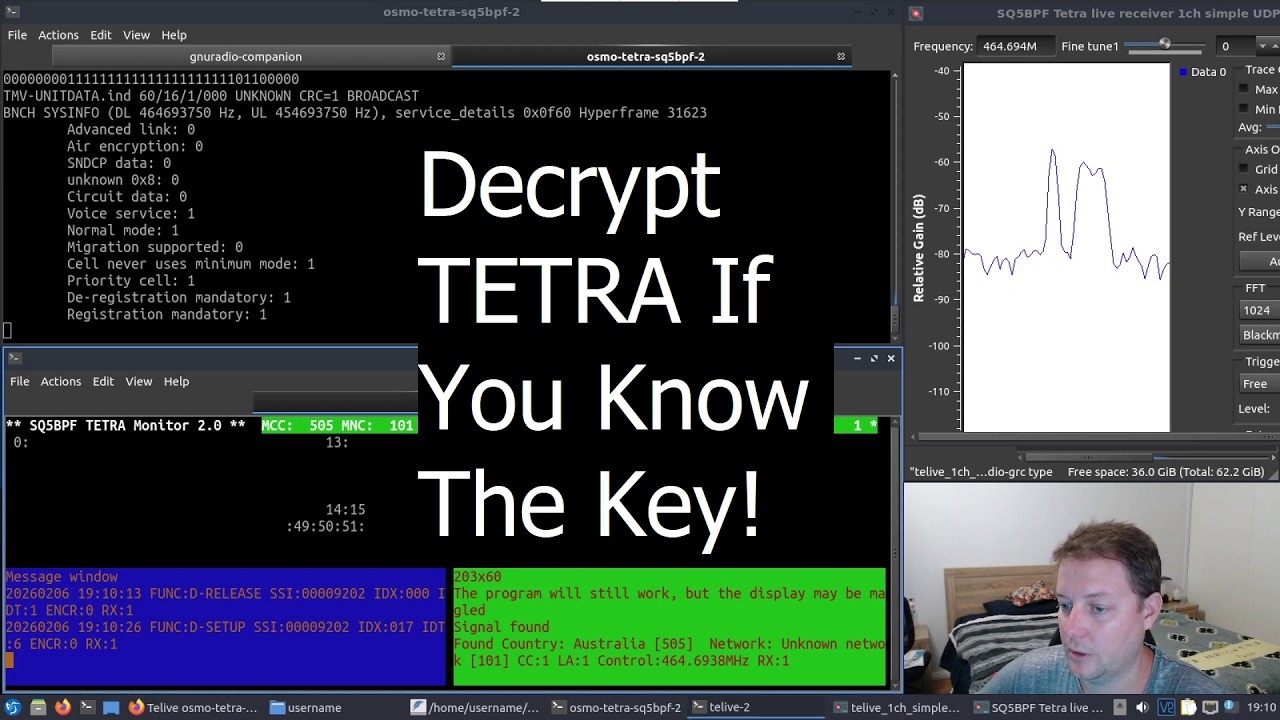
TELIVE-2: An Upgrade In TETRA Decoding That Allows For Voice Decryption (If You Have The Key....)
Автор: Rob VK8FOES
Загружено: 2026-03-17
Просмотров: 285
Описание:
NOTE: TELIVE-2 CAN ONLY LISTEN TO ENCRYPTED TETRA VOICE IF THE KEY IS ALREADY KNOWN!!!
I'm a bit late to the party with this one fellas, but better late than never I guess! TELIVE is the foundation of essentially all open-source TETRA radio decoding tools in both Windows and Linux. It was so groundbreaking in fact, that the Osmocom guys rebased their entire 'osmo-tetra' project with code from Jacek Lipkowski's famous TELIVE software suite from 2014. Development stalled for many years until late in 2025, when a surprising git commit added support for voice decryption using a reduced-size 32-bit key.
But what exactly does this mean? 32-bit key size is the cipher key length of the famous TEA-1 backdoor discovered by Team Midnight Blue in 2023. Suspected to be the result of the United States' NSA organization pressuring ETSI, it allows a TEA-1 encryption key to be reduced in size from 64-bit to a measly 32-bit. This will of course allow for brute force dictionary attacks to recover the key in minutes on modest computer hardware!
Please understand that TELIVE-2 does NOT ALLOW for cracking of the TEA-1 algorithm in TETRA radio. It is only a decryption tool if the key is ALREADY KNOWN. Cracking and decrypting are two separate processes, and currently there are no publicly released tools that aid in the cracking phase thus far. However, I don't think it's coincidental that these decryption tools are all of a sudden bursting onto the scene. It smells to me like somebody has turned Team Midnight Blue's research into a real-world practical method and software tool... But what would I know ;)
Thanks very much for watching!
COMMANDS:
cd
git clone https://github.com/sq5bpf/osmo-tetra-...
cd osmo-tetra-sq5bpf-2/src
make -j$(nproc)
cd
git clone https://github.com/sq5bpf/telive-2.git
cd telive-2
make -j$(nproc)
cd ~/osmo-tetra-sq5bpf-2/etsi_codec-patches
./download_and_patch.sh
cd ../codec/c-code
make -j$(nproc)
cp -v cdecoder sdecoder ~/telive-2/bin
(Substitute two heart❤︎ symbols for greater-than signs)
echo 'export PATH=$PATH:/home/username/telive-2/bin' ❤︎❤︎ ~/.bashrc
nano ~/telive-2/bin/tplay
cat $* | /home/username/telive-2/bin/cdecoder /dev/stdin /dev/stdout | /home/username/telive-2/bin/sdecoder /dev/stdin /dev/stdout | aplay -fS16_LE
cd
wget https://raw.githubusercontent.com/osm...
gnuradio-companion telive_1ch_simple_gr310_udp.grc
cd ~/osmo-tetra-sq5bpf-2/src
./receiver1udp 1
cd ~/telive-2
./telive
DISCLAIMER: Interception of telecommunications is prohibited in Australia under the Telecommunications (Interception and Access) Act 1979. Chapter 2, part 2-1, section 7, subsection 1, parts (a), (b), and (c) state: 'A person shall not intercept, authorize, suffer or permit another person to intercept, or do any act or thing that will enable him or her or another person to intercept a communication passing over a telecommunications system.'
This video was recorded and uploaded for the express purposes of education and experimentation. Intercepting and decrypting secure radio communications is prohibited by law in most jurisdictions, and I can not be held responsible for any legal ramifications experienced as a result of recreating the steps in this video.
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: