Kerberos Deep Dive Part 4 - Unconstrained Delegation
Автор: Compass Security
Загружено: 2025-09-11
Просмотров: 426
Описание:
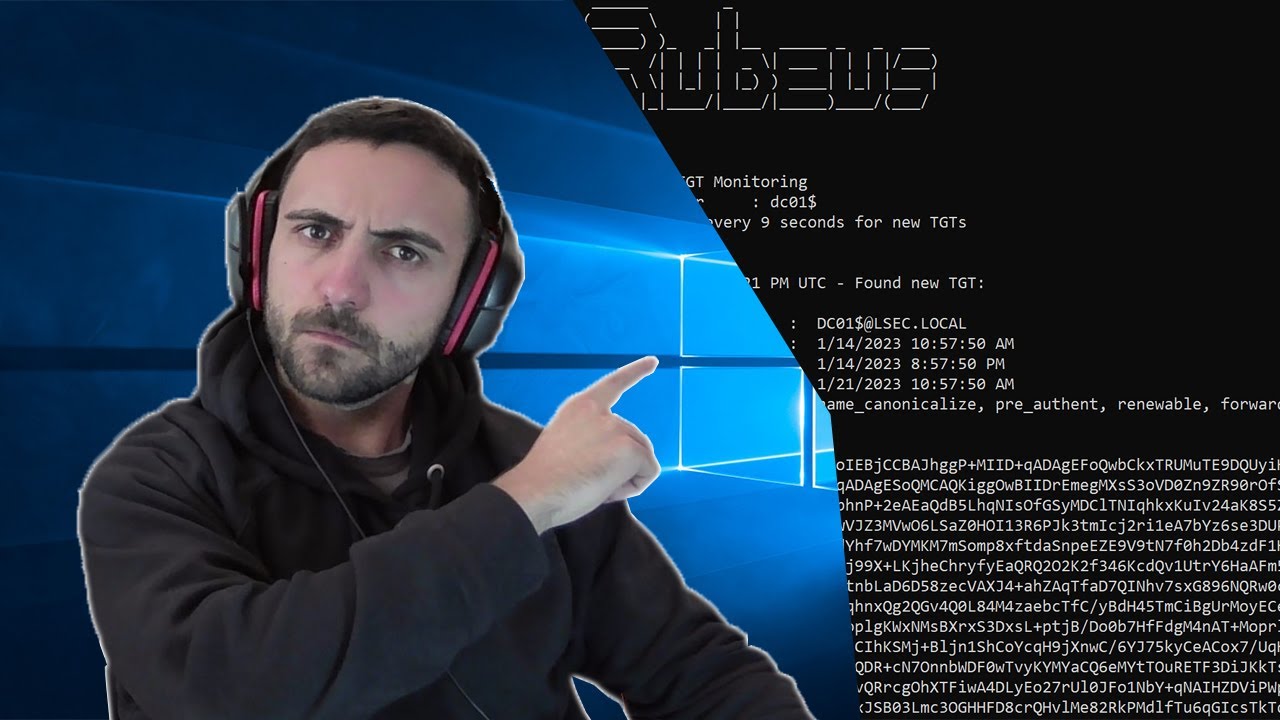
Delegation is a powerful mechanism in Kerberos to allow user impersonation. Unconstrained delegation can expose high-value credentials to attackers with local admin access. This episode explains how it works, the real-world abuse scenarios, and how to audit and lock down systems vulnerable to this legacy feature.
The slides shown in the video can be found here: https://www.compass-security.com/de/r...
0:00 Introduction
1:29 Delegation Basics
4:48 Sensitive Users
6:16 Protected Users
9:17 Kerberos Basics
10:59 Unconstrained Delegation
14:41 Configuration
17:34 Security Risks
19:44 Attack Basics
26:03 Triggering Connections
28:42 PrinterBug to Domain Admin
34:30 Recommendations
37:32 TGT Copy Mechanism
45:35 Session Keys
55:04 TGT Delegation Abuse
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: