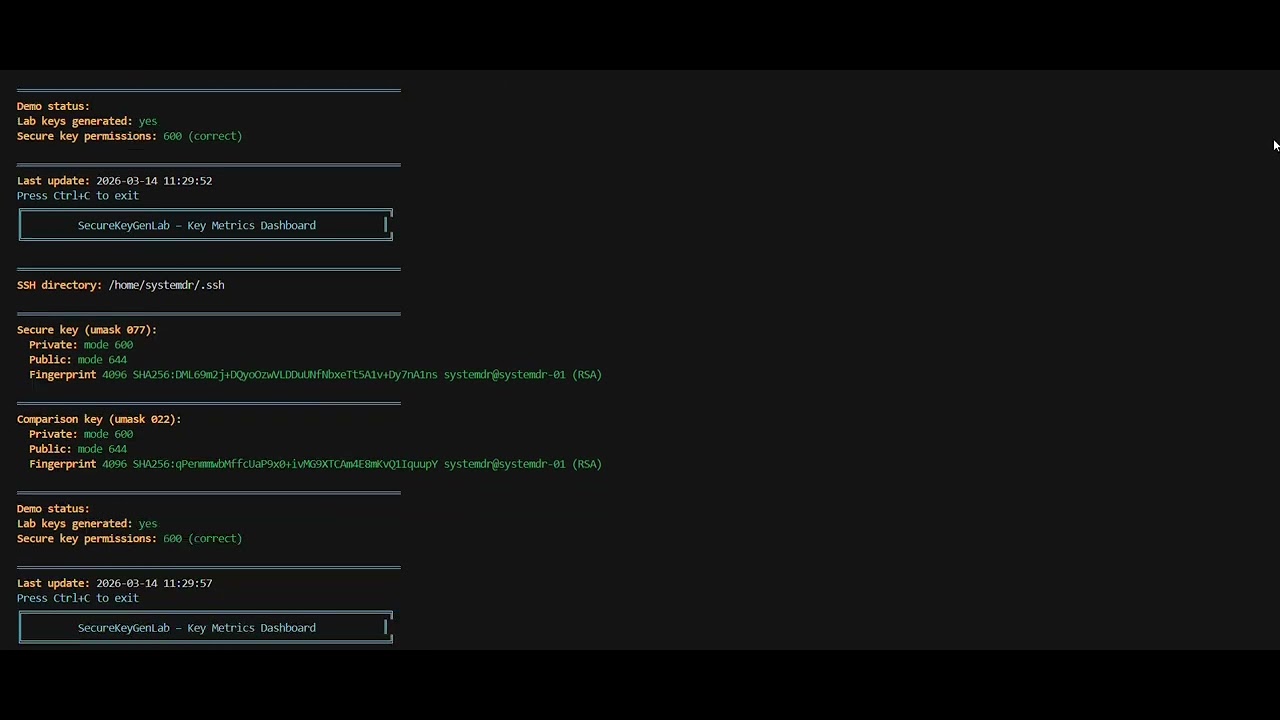
Day 18: Generating Keys with Strict Permissions (umask 077) – The Invisible Shield for Your Secrets
Автор: SystemDRHandsOnCourseDemo
Загружено: 2026-03-14
Просмотров: 1
Описание:
Welcome back, architects of the digital frontier. Today, we're not just learning a command; we're embedding a critical security philosophy into the very fabric of our home lab infrastructure. You've hardened your baseline install; now, let's talk about the guardians of your system's identity: cryptographic keys.
In the world of ultra-high-scale systems, where a single leaked secret can cascade into a global incident, every engineer needs to understand not just how to generate keys, but *how to generate them securely*. This isn't just theory; it's a non-negotiable prerequisite for building anything robust.
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке:



















