Malware Analysis - Hybrid Analysis for Malware Assessment
Автор: MalwareAnalysisForHedgehogs
Загружено: 2022-07-30
Просмотров: 7744
Описание:
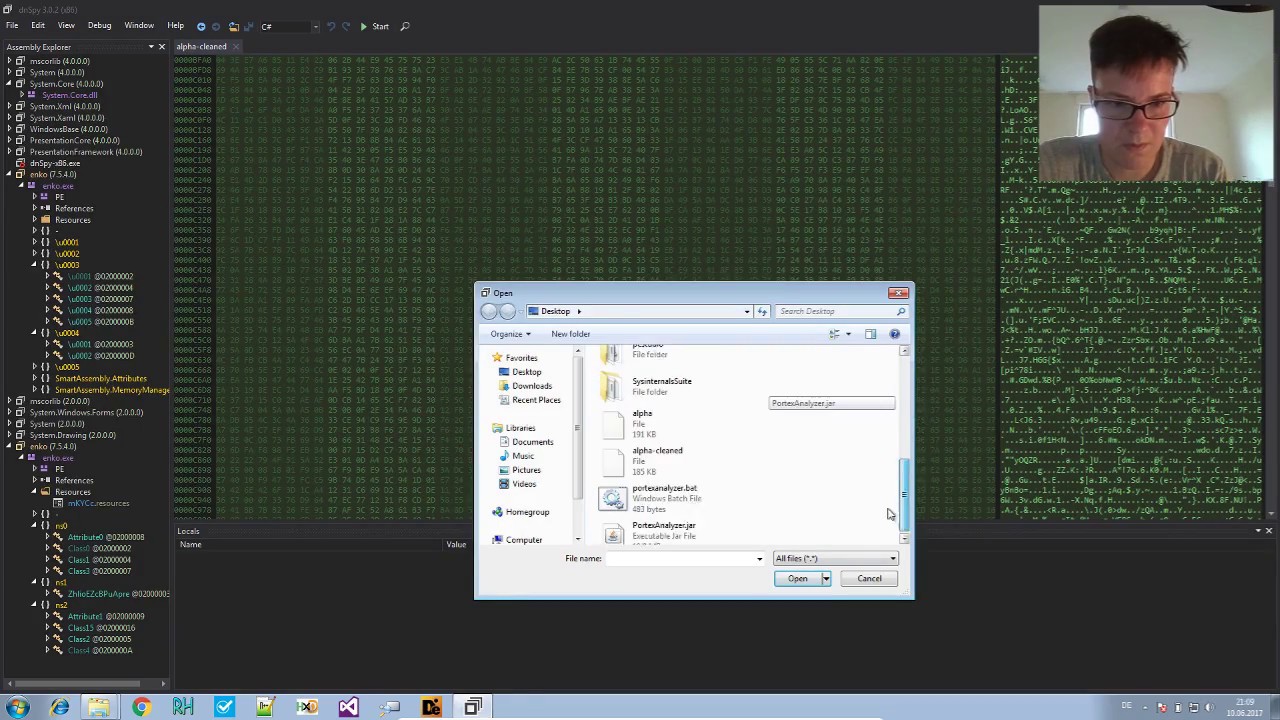
Automatic sandbox systems like Hybrid-Analysis are a great way to speed up malware analysis. We find a file flagged as keylogger that has almost no antivirus detections.
Report: https://www.hybrid-analysis.com/sampl...
Malware analysis courses: https://malwareanalysis-for-hedgehogs...
Buy me a coffee: https://ko-fi.com/struppigel
Follow me on Twitter: / struppigel
00:00 Introduction
00:17 What is Hybrid Analysis, hunting undetected malware
04:28 Sample flagged as keylogger, things I look at first
05:45 File Details: Hashes explained
09:47 File Details: compiler, version info, icon, PortEx visualization
14:40 File Sections
14:58 File Imports: when is ImpHash useless
15:23 Screenshots: conclusions related to risk assessment
17:00 Processes, API calls, was there process injection
19:17 Network Analysis
19:32 Why was it flagged as keylogger
20:42 Extracted Strings: UAC bypass?
22:04 Dropped Files
25:05 Malicious Indicators
27:05 Suspicious Indicators
33:46 Summary: Is this file malicious? How to proceed with analysis?
35:09 Summary: General tips for malware analysis with sandbox systems
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: