What Is The OWASP Mobile Top 10?
Автор: UnderSecured
Загружено: 2025-01-06
Просмотров: 2587
Описание:
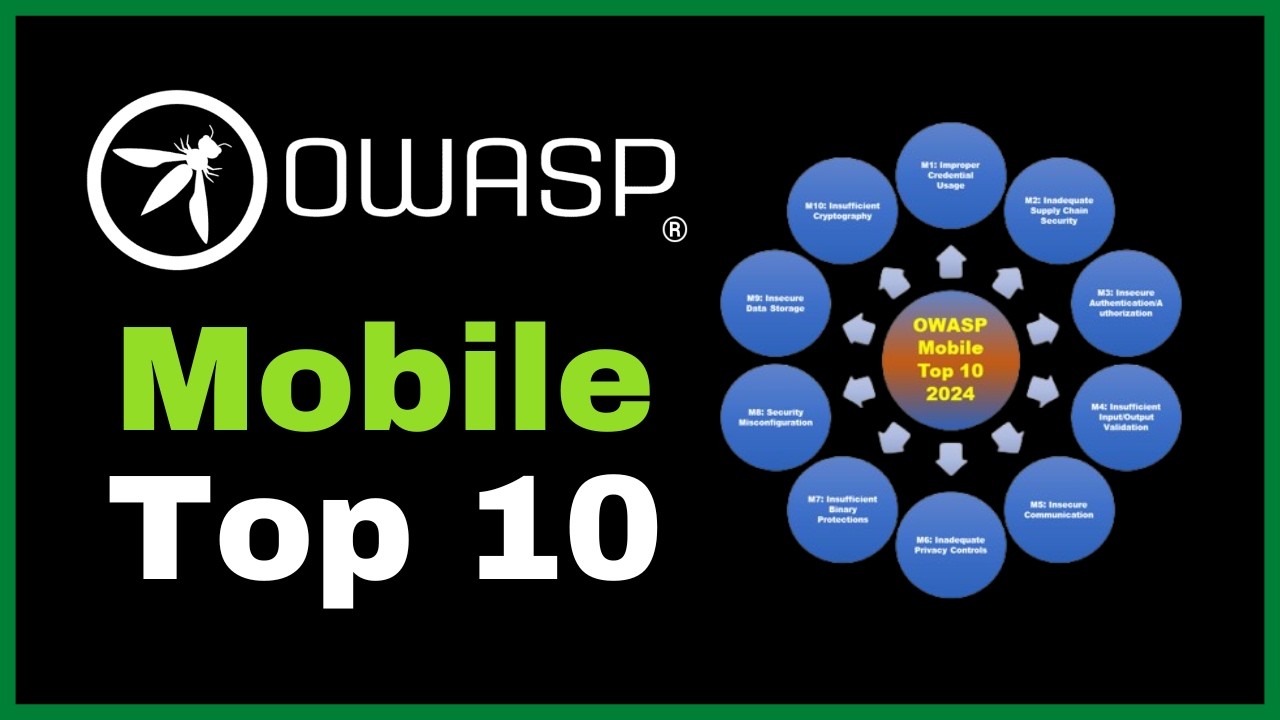
When pentesting or hacking mobile applications, it can sometimes be difficult to know what you should spend your time on. Fortunately, OWASP puts out a top 10 list every few years with the top 10 most important categories for vulnerabilities that we should be paying attention to. In this video, I go over all 10 categories of the OWASP Mobile Top 10 and go over some examples of the types of vulnerabilities that you should be looking for in each category.
0:00 Intro
1:19 Improper Credential Usage
3:30 Inadequate Supply Chain Security
4:41 Insecure Authentication/Authorization
6:42 Insufficient Input/Output Validation
8:05 Insecure Communication
11:25 Inadequate Privacy Controls
12:52 Insufficient Binary Protection
14:39 Security Misconfiguration
16:32 Insecure Data Storage
18:05 Insufficient Cryptography
19:37 Outro
You can find the OWASP Mobile Top 10 list here: https://owasp.org/www-project-mobile-...
https://corsecure.blog
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: