Google Pixel FAILED This Security Test (LEAKED)
Автор: Explaining Android
Загружено: 2025-11-15
Просмотров: 2767
Описание:
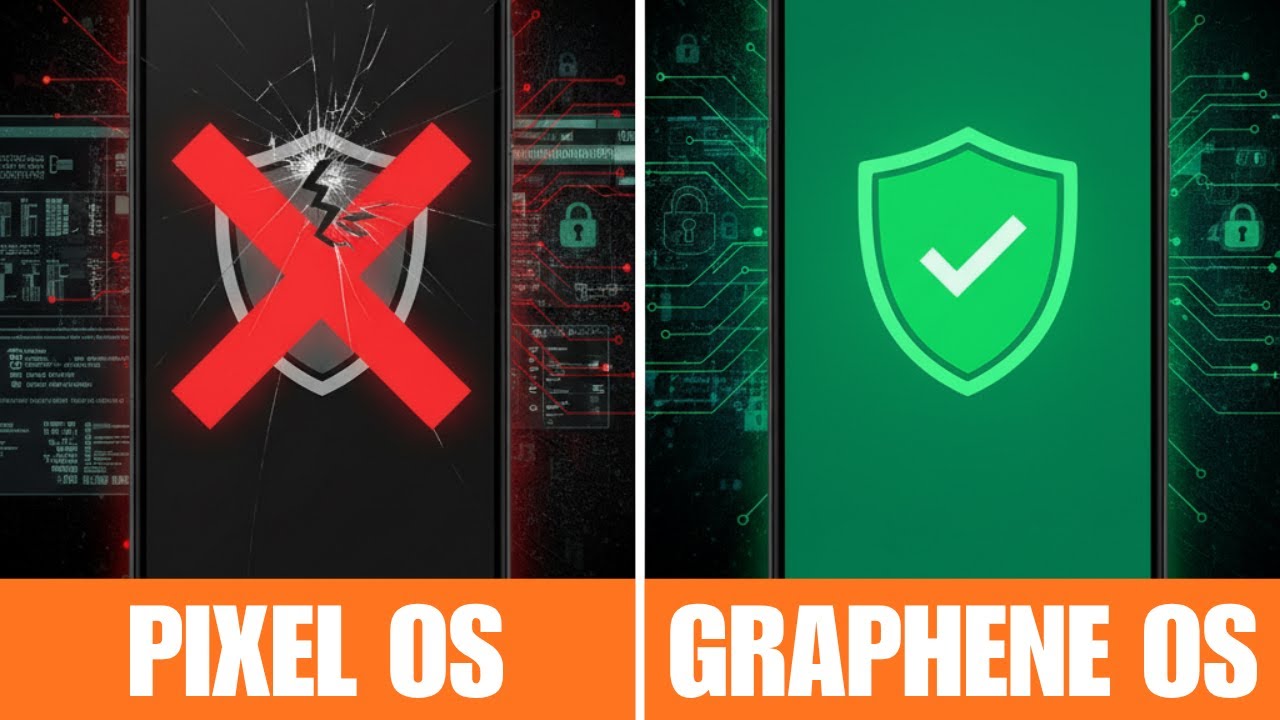
A leaked image from Cellebrite suggests they can access data on Pixel OS much more easily than GrapheneOS.
~~~~~
Hi! Don't forget to like the video, subscribe to the channel, and hit the "Thanks" button on this video, if you can, and join our channel community here - / @explainingandroid
Links
~~~~~~~
GrapheneOS Thread - https://discuss.grapheneos.org/d/2769...
Video Description
~~~~~~
Cellebrite is a digital forensics company that provides tools to various law enforcement agencies. . .and even enterprise companies. Google tells us that these tools allow the customer to extract, analyze, and manage data from mobile devices, computers, and the cloud.
But some phones are going to be more secure than others.
And there's been a new leak that suggests Google's own Pixel OS is more vulnerable to these tools from Cellbrite than if you were to install GrapheneOS.
Let's take a look at this table.
#android #grapheneos #android16 #android15 #googlepixel
Google Pixel Security
From what I have read, this leak came to us from an anonymous individual who was able to quietly sit in on a virtual Cellebrite briefing. During this Microsoft Teams meeting, we're told this screenshot was shared among the participants.
And in this image, we see a table that allegedly shows how vulnerable Google Pixel phones are.
But it seems as if the security focused GrapheneOS firmware is so popular these days. . .that the folks over at Cellebrite decided to add it to their support matrix table.
Here's what the table tells us.
We have 4 different rows here.
One for the Pixel 6 series.
One for hte Pixel 7 series, plus the pixel fold and hte pixel tablet.
one for hte pixel 8 series
and one for the pixel 9 series.
Then, we have columns for the various states that an Android phone can be in.
So there's a standard operating system while in a BFU state (before first unlock)
then a column for the standard operating system in an afu state (after first unlock)
and lastly, there's one for the standard operating system in an unlocked state
then we have those three states repeated. . .but with GrapheneOS installed as the firmware. . .instead of Pixel OS.
According to this table.
Cellbrite has no problem accessing personal data from every pixel deivce since the pixel 6
no matter if it's before the first unlock. . .after the first unlock. . .or when the device itself is unlocked.
It's only until we get to the GrapheneOS columns, that we see. . .
pixel 6 series and pixel 7 generation devices. . .as long as have current security patches installed, then your data is said to be safe. because they can only get to the data until the user installed a late 2022 security update
pixel 8 series devices are wide open it seems. . .giving access to the full filesystem
and right now, the pixel 9 series. . .at least from what this table tells us
is completely safe. . .but only if you have grapheneOS installed
conclusion
there's been a lot of talk lately about how GrapheneOS is the favorite mobile operating system for criminals
which, to me, is like tying the Signal application to criminal activity.
just because you have grapheneOS installed. . .doesn't make you a criminal
just like using signal doesn't mean your communicating about illegal topics
it just means you value your privacy and you'll do what you can to prevent that data from getting into the hands of big tech.
1. Intro [00:00]
2. Leaked Cellebrite Access Table [00:48]
3. Closer Look at the Details Revealed [01:42]
Step by Step Tutorial
~~~~~
1. Intro [00:00]
2.
As an Amazon associate, I may earn a commission on sales from the links below.
The Gear I Use
~~~~~
5W "Slow" Charger - https://amzn.to/2OaUMV8
Fast Charger - https://amzn.to/3rtBsC6
MicroUSB Cable - https://amzn.to/38dkpeM
USB-C Cable - https://amzn.to/2OqlTvi
TPU Cases - https://amzn.to/38g9b9w
USB-C to 3.5mm Dongle - https://amzn.to/3rVt7c3
USB-C to 3.5mm DAC - https://amzn.to/3CyksSJ
NVIDIA Shield TV - https://amzn.to/4cZFaJz
Telescopic Controller - https://amzn.to/3uDrvY9
Повторяем попытку...
Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: