From Alert to Resolution: Using Security Agents to Power Real‑World SOC Workflows
Автор: Microsoft Security Community
Загружено: 2026-02-25
Просмотров: 601
Описание:
Wednesday, Februray 25th 2026 | 8:00AM – 9:00AM (PT, Redmond Time webinar recording date)
Microsoft Security Store | From Alert to Resolution: Using Security Agents to Power Real‑World SOC Workflows
Presenters: Pablo Chacon, Ankur Arora, Ugur Koc, and Konrad Sagala
Description:
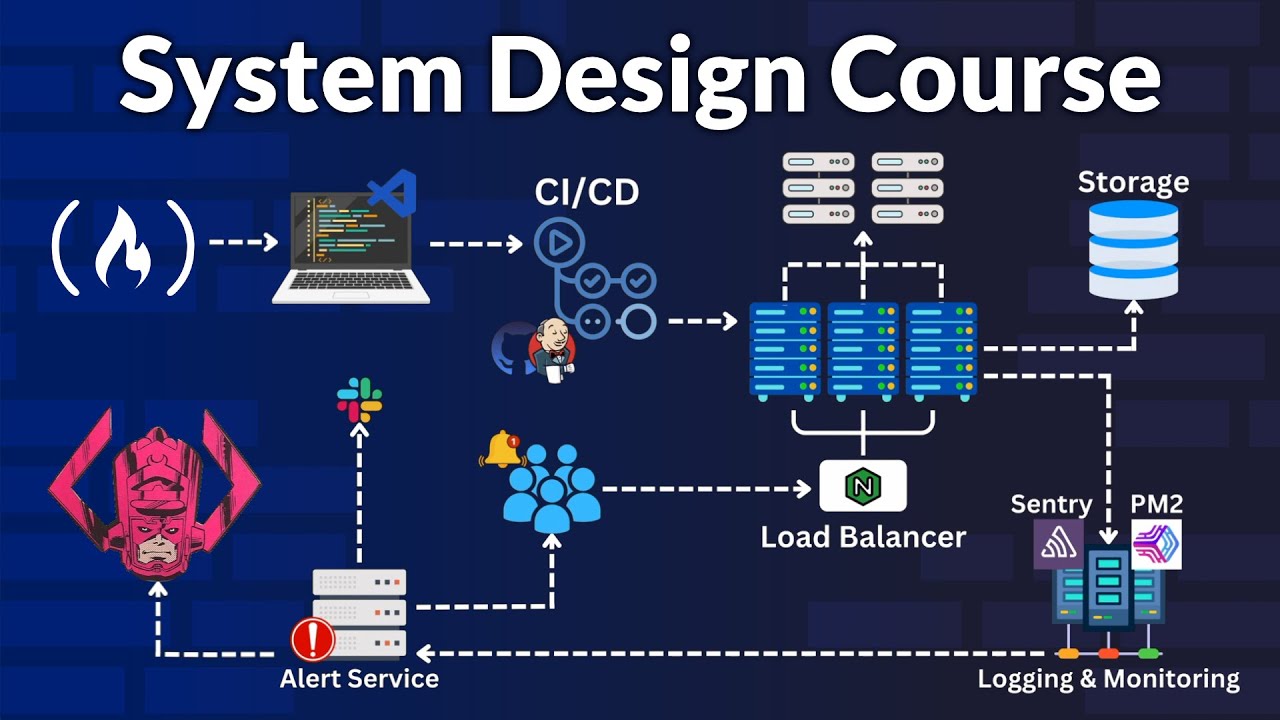
In this webinar, we’ll show how SOC analysts can harness security agents from Microsoft Security Store to strengthen every stage of the incident lifecycle. Through realistic SOC workflows based on everyday analyst tasks, we will follow each scenario end to end, beginning with the initial alert and moving through triage, investigation, and remediation. Along the way, we’ll demonstrate how agents in Security Store streamline signal correlation, reduce manual investigation steps, and accelerate decision‑making when dealing with three of the most common incident types: phishing attacks, credential compromise, and business email compromise (BEC), helping analysts work faster and more confidently by automating key tasks, surfacing relevant insights, and improving consistency in response actions.
Timestamps:
00:00 – Introduction
03:17 – Discovering, buying, and setting up Security Agents
Responding to SOC scenarios assisted by security agents
12:15 – Demo 1: Phishing attack scenario
24:54 – Demo 2: Account takeover / Business email compromise
40:50 – Close
Discover, try, activate Security Agents today!
Visit the Microsoft Security Store at : https://securitystore.microsoft.com/a...
For Partners: Toolkit for creating and publishing Security Copilot Agents: http://aka.ms/SecurityCopilotDevelope...
Coming to RSA Conference 2026? Let’s meet: https://aka.ms/MeetUsAtRSA
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке: