DEF CON 30 - Sam Quinn, Steve Povolny - Perimeter Breached Hacking an Access Control System
Автор: DEFCONConference
Загружено: 2022-10-17
Просмотров: 33123
Описание:
The first critical component to any attack is an entry point. As we lock down firewalls and routers, it can be easy to overlook the network-connected physical access control systems. A study done by IBM in 2021 showed that the average cost of a physical security compromise is $3.54 million and takes an average of 223 days to identify a breach.
HID Mercury is a global distributor of access control systems with more than 20 OEM partners, deployed across multiple industries and certified for use in federal and state government facilities.
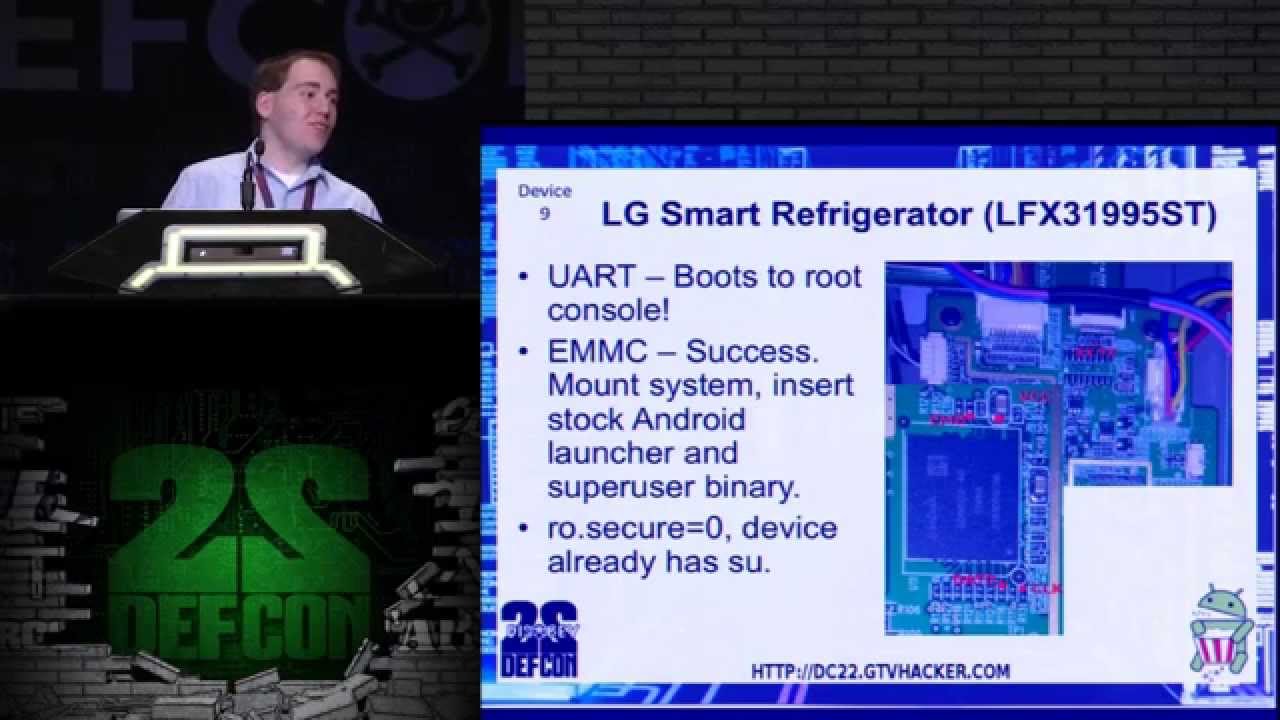
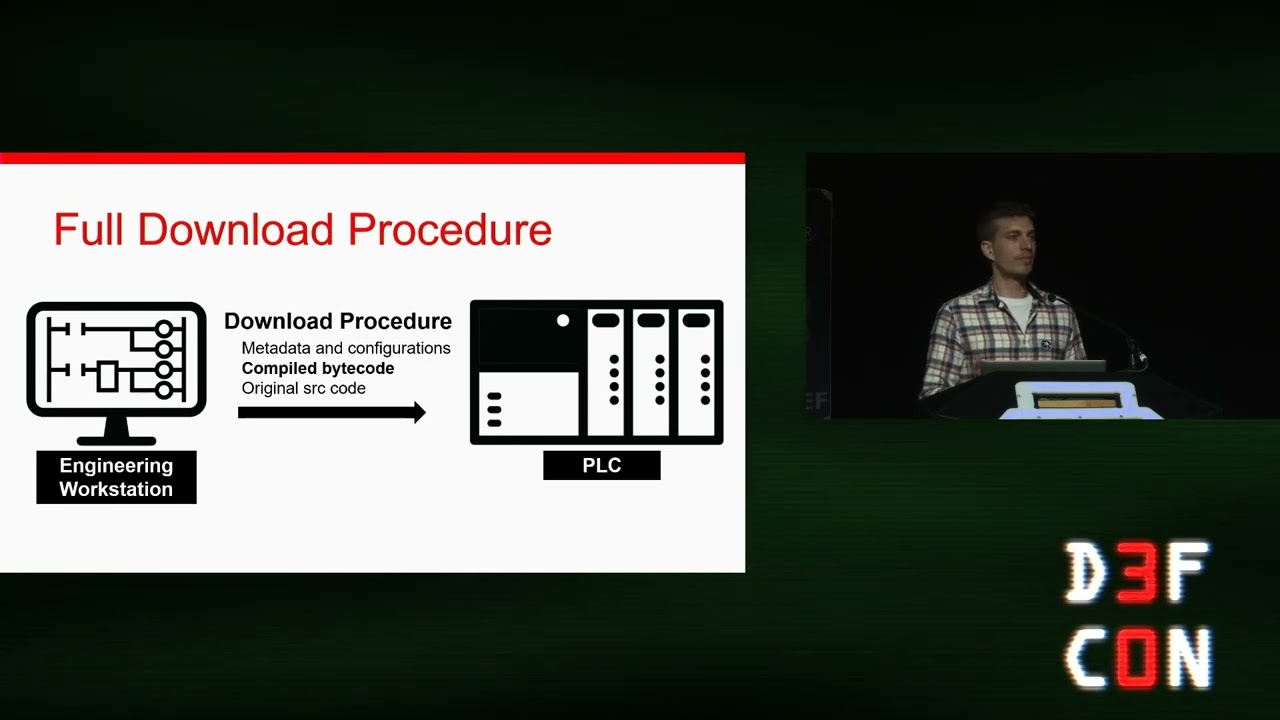
Trellix's Advanced Threat Research team uncovered 4 unique 0-day vulnerabilities and 4 additional undisclosed vulnerabilities leading to remote, unauthenticated code execution on multiple HID Mercury access control panels. These findings lead to full system control including the ability for an attacker to remotely manipulate door locks. During this presentation, we will briefly cover the hardware debugging process, leading to a root shell on the target. We will explore in greater depth the vulnerability discovery techniques, including emulation, fuzzing, static and dynamic reverse engineering, and a detailed walkthrough of several of the most critical vulnerabilities. We’ll address our approach to exploitation using simplistic malware we designed to control system functionality and culminate the talk with a live demo featuring full system control, unlocking doors remotely without triggering any software notification
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке:
![[1040] Fingerprint/RFID Lock Defeated With a Paperclip (Mengqi-Control)](https://imager.clipsaver.ru/z4lVylO7y5U/max.jpg)