Floxif File Infector with Control Flow Obfuscation Analysis (Stream - 06/01/2026)
Автор: Invoke RE
Загружено: 2026-01-13
Просмотров: 1188
Описание:
Throughout this stream we analyze a Floxif file infector that uses control flow obfuscation with Binary Ninja. We use Binary Ninja's Python API to patch control flow obfuscation routines to recover the original control flow and started to learn the custom string constants API introduced in 5.2 https://binary.ninja/2025/11/13/binar...
Learn how to reverse engineer malware: https://training.invokere.com/
Merch: https://shop.invokere.com/
Stream code, binaries and databases available with Premium: https://training.invokere.com/course/...
Twitch: / invokereversing
Twitter: / invokereversing
BlueSky: https://bsky.app/profile/invokerevers...
Mastodon: https://infosec.exchange/@invokerever...
00:00 Introduction and Floxif Overview
04:43 Floxif Control Flow Obfuscation
13:11 Patching Control Flow Obfuscation
22:02 Automating Control Flow Patching
24:16 VM Hardening Tangent
27:37 Automating Patching Continued
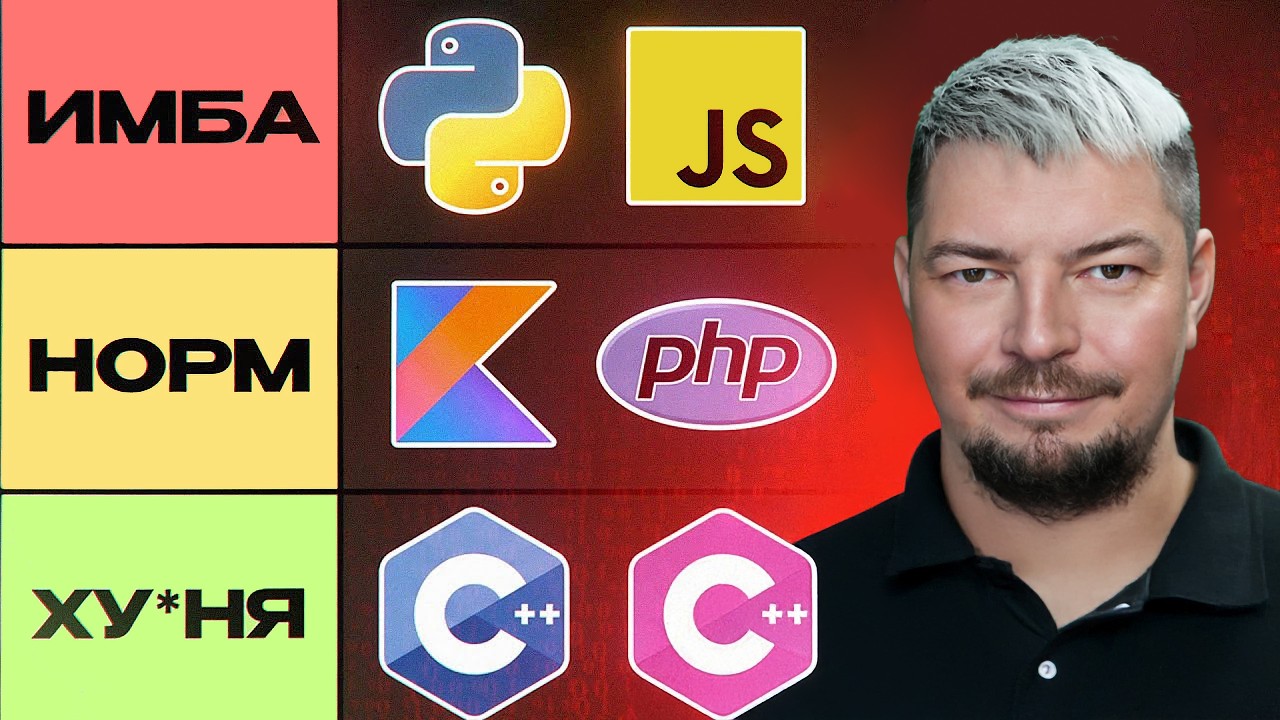
36:03 C++ discussion
42:13 Reversing String Decrypt Struct
49:19 XOR String Decryption
1:00:43 Learning the Custom String Constants API
1:18:13 Outro
Повторяем попытку...

Доступные форматы для скачивания:
Скачать видео
-
Информация по загрузке:





![AI in Cyber Security: The Storm and the Compass [KEYNOTE] by Joshua Reynolds at BSides Edmonton 2025](https://imager.clipsaver.ru/tLR_hHQVkOk/max.jpg)









![Собеседование Python Junior разработчик [2026]](https://imager.clipsaver.ru/zibAC8HkGFk/max.jpg)


